Summary
While some of our team were at Gartner IAM and SecureWorld Boston last week, the Oort Identity Security Platform continued to grow! This week, you’ll benefit from new dashboard updates, extra IP-based context, and a new check that helps to ensure your Salesforce is tied to your SSO.
📈 Dashboard Updates
Since we released the Identity Security Dashboard last week, we’ve already been busy taking your feedback on board and adding new components. This week, you’ll notice two main updates:
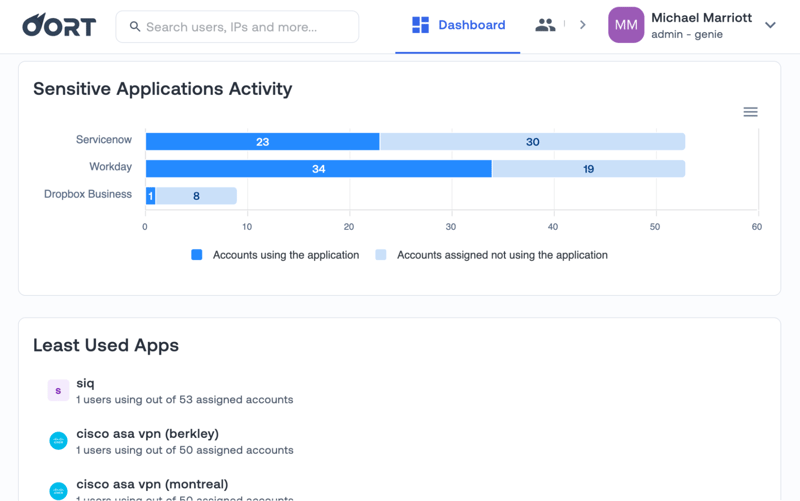
1. Sensitive Application Activity. Within the initial dashboard release, we displayed the least used applications. In this release, we’ve included a specific component for sensitive application activity. This displays the distribution of assigned accounts using and not using the application. Given that these applications are sensitive, access should be reassessed if many assigned accounts are not using the applications.
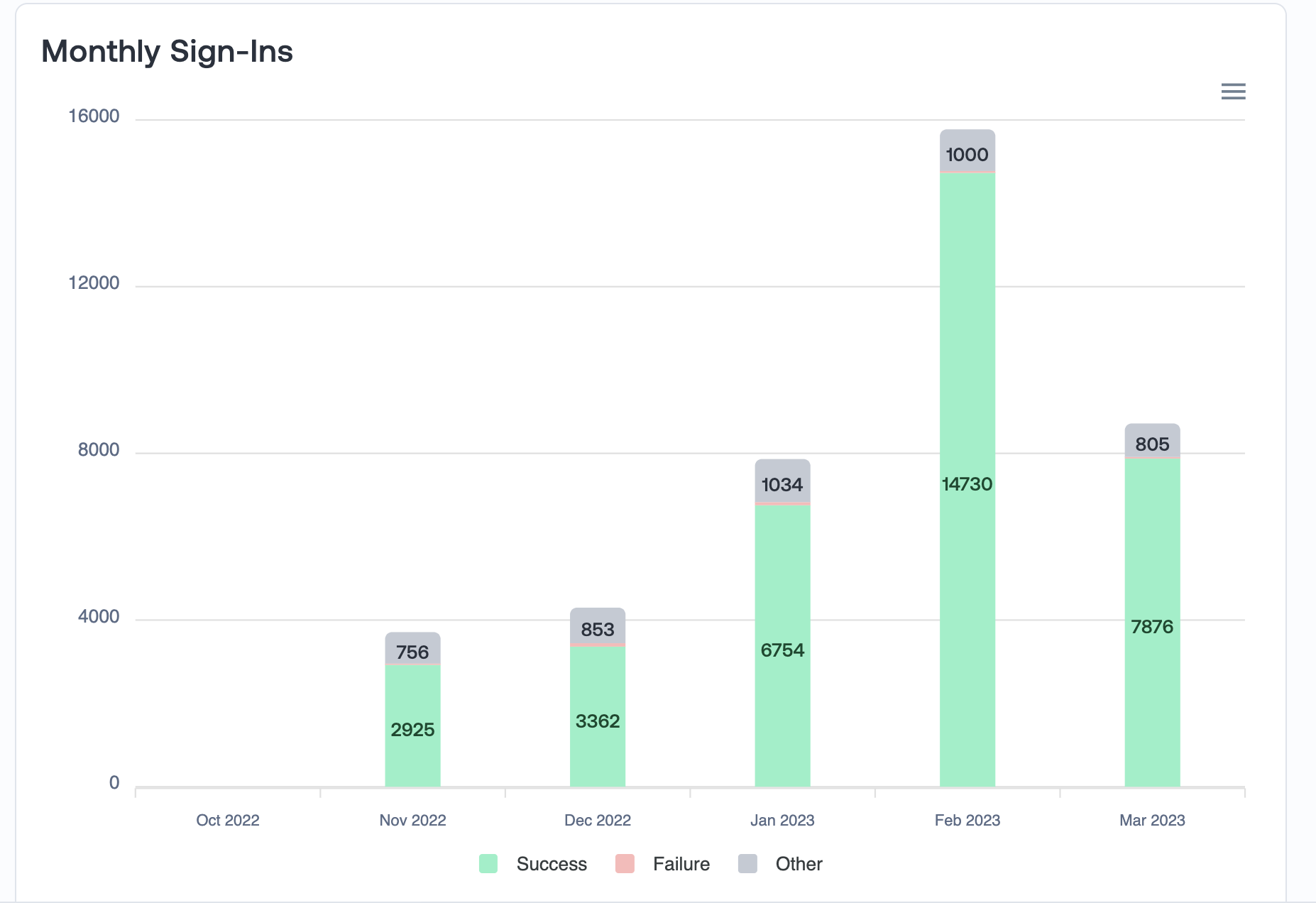
2. Monthly Sign-In Activity. Several of our checks provide insights into IP probing and password spraying attacks. When you’re trying to understand what “normal” looks like, it can be helpful to have a month-to-month baseline of successful and unsuccessful login attempts. This new component visualizes failed and successful login activity on a monthly basis.
Furthermore, for those who love the dashboard and want to land on it by default with every log-in, you can change your settings in Tenant Settings - Landing Page.

✅ Ensure Salesforce Access is Through SSO
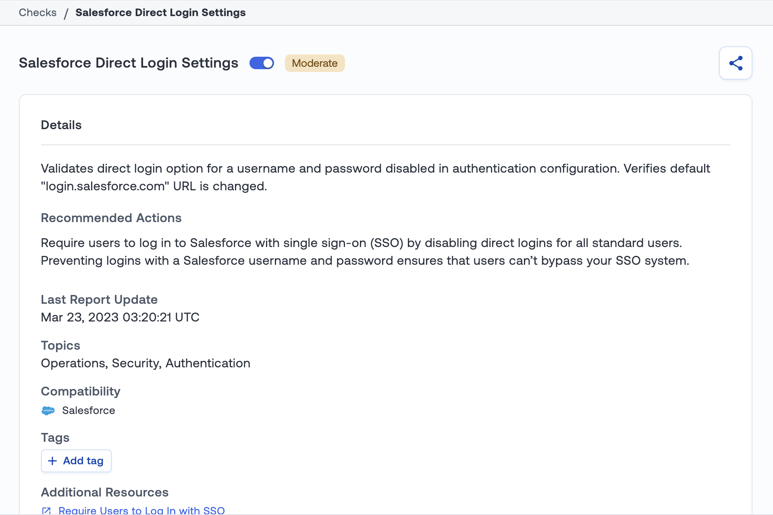
Over the past few months, we’ve been releasing more and more ways to understand risks associated with Salesforce access. For example, several weeks ago, we released the ability to detect when Salesforce logins bypass SSO.
When companies enforce SSO for Salesforce, this should ensure that users can no longer access the application with a username and password.
In our latest release, we have a new check to detect that these settings are in place - “Direct Log On to Salesforce Settings.” This check will detect if there is still an option to sign in with a username and password.
🌐 More IP Info in Networks
We’re frequently updating our User 360 profiles so that you have the richest context for every identity in your population. Within the Networks section of the user profile, we have added context on IP addresses that will be helpful in an investigation. To access this context, simply click on the relevant row, and a side panel will appear with information on the ASN, ASN Domain, ASN Name, ASN Type, and ASN Country.
Bug Fixes and Minor Improvements
- Disabled users. We will no longer evaluate checks for disabled users.
- Azure Blocked Requests. We now recognize blocked requests from Azure Active Directory.


