Identity Threat Detection and Response (ITDR) is a hot topic in 2022, with Gartner having published multiple pieces of research on the subject (see Top Trends in Cybersecurity 2022 and Enhance Your Cyberattack Preparedness With Identity Threat Detection and Response).
Given how many breaches take advantage of identity weaknesses, it’s great to see that such serious research is taking place. However, for every security team weighing whether they should invest in these capabilities for 2023, it’s also important to remember that ITDR is just one part of an overall Identity Security strategy.
Seven Identity Attacks to Bypass MFA
It’s no surprise that identity is at the forefront of the conversation given the number of major security breaches in 2022 that have featured identity at their core.
Identity-based attacks range in their sophistication, but it doesn’t take much to get started. Using a combination of social engineering and phishing has enabled attackers to steal username/password credentials and then try one of many techniques get past MFA:
1. MFA Fatigue. The attacker simply relies on victims being conditioned to always press the “allow” button on their phone when a push notification comes up.
2. MFA Flooding. The attacker keeps hitting the “push” notification until sometime around 3:23 AM the victim finally gets tired of it and hits the allow button so they can sleep.
3. MFA Reset. The attacker calls into the victim’s IT Helpdesk and says “I lost my phone, can you please reset my account so I can sign-in and get my work done?” This then allows the attacker to either enroll a new factor upon sign-in or to persist during generous “grace” periods allowed by MFA policy.
4. Asking nicely. The attacker impersonates someone from the victim’s IT department (potentially after spamming them with MFA push notifications) and suggests that the victim either press the “allow” button or share the one-time passcode so the MFA flooding issue with their account can be resolved (or some other excuse). Phishing, smishing, vishing - the idea is the same.
MITM Proxy. The attacker sets up a login page that looks and feels like the real single sign on (SSO) and the victim unwittingly enters not only their username/password (common for phishing attacks) but also their one-time passcode. Or perhaps a push notification comes through at around the same time as they enter their credentials into the phishing site and they hit “allow” on their phone thinking that the request originated from their own device when in fact the attacker simply entered the stolen credentials into the real login page either via swivel chair or automation.
SIM Swapping. The attacker calls up the victim’s mobile carrier to switch the phone number of the victim to a new SIM card in the attacker’s possession. Now any 6-digit SMS codes will arrive on the attacker’s device.
0ktapus style. Finally, if you’re really committed, go compromise the Twilio account of your victim’s messaging app (e.g. Signal) to sniff SMS messages on their way to the victim’s device.
Detection versus Prevention
Can ITDR detect some of these techniques? Yes.
A good ITDR solution will detect and sometimes even block these types of attacks before they get very far.
Can ITDR prevent them? No.
That’s where proactive identity security comes in. A complete and comprehensive identity security platform must include the following three capabilities:
Identity Attack Surface Mapping - ingests identity data from across your entire architecture to discover the swirling mass of identities that orbit your enterprise. Identity attack surface mapping gives your team an understanding of what’s out there - how many identities you have in your population, the demographics of the population, and how it might be changing over time. The attack surface changes day-to-day as identities join and leave your organization, so this must be a continuous process.
Identity Security Posture Management - examines the identity attack surface to find vulnerabilities. Specifically, accounts that are vulnerable to account takeover. An inactive account that no one has used in months is no different than an unused, unpatched server sitting in a forgotten closet somewhere. It’s an easy entrypoint, made even easier for the attacker if that account has not had a password rotated in years and has no second factor configured. Posture management not only finds these vulnerabilities, but recommends and even implements campaigns to clean them up - effectively “patching” your identities.
Identity Threat Detection & Response - finally ITDR picks up where the others leave off. No matter how perfect your IAM architecture might be and how many proactive and preventative measures you might take, something will always get through. ITDR is the last line of defense, to detect techniques and behaviors that might indicate a successful account takeover has taken place (or is in progress).
Identity is the new perimeter and only this combination of capabilities can offer an end-to-end approach to securing that perimeter. A mature identity security program includes all three and, for organizations large enough, an identity security expert who ensures that they’re implemented properly.
Infrastructure Needs Security
Can’t I do this with my existing IAM stack? Not really.
Can you configure your router to act like a firewall? Maybe. Should you? Probably not.
Can you rely on OS-packaged endpoint protection? Sure. Should you? It depends.
Oftentimes IT infrastructure vendors will package basic security capabilities in their products to serve the majority of small and mid-size businesses that don’t require a full-blown Palo Alto or Cisco firewall or a Crowdstrike EDR. IAM infrastructure includes some security features too.
IAM infrastructure is typically comprised of some combination of the following technologies:
-
Directory - the database of identities and their profiles, group membership, etc. Typically a reflection of your HR system and your vendor management system. Microsoft Active Directory is the most common directory solution for large organizations.
-
SSO - single sign-on enables users who are defined in your directory to sign in to multiple applications with a single account. Implements protocols like SAML and OIDC. Okta and Microsoft Azure AD dominate this market today.
- MFA - augments your SSO infrastructure with additional authentication factors (including but not limited to passwordless, push notifications, and device trust). Cisco Duo is a prime example of an MFA provider.
-
IGA - identity governance and administration comes into play when companies need to audit and automate how roles and permissions are assigned within the organization and to solve the joiner-mover-leaver lifecycle for identities. IGA traditionally also provisioned accounts in applications that did not support SCIM-based provisioning, but that is less of a need today other than for legacy applications. Well-known players include SailPoint and Saviynt.
-
PAM - privileged access management helps to protect accounts that don’t fit neatly into the SSO system such as root and admin accounts for applications and devices. These are highly privileged accounts that require an extra layer of protection, usually in the form of a password vault, to prevent them from falling into the wrong hands. CyberArk and Delinea (merger of Thycotic and Centrify) are common examples.
Every one of these technologies is infrastructure - just as much as your company devices and your company network are infrastructure, so too are your Directory, SSO, MFA, IGA, and PAM solutions part of your IAM infrastructure. They’re the plumbing of the identity world.
Infrastructure needs security. You can’t rely on your devices, your networks, your applications, or your data to secure themselves. Identity is no different. Relying on IAM infrastructure to secure itself invariably leads to your SSO vendor as a single point of failure in your enterprise security architecture. This mistake has led to the rise of identity-based attacks. Attackers are effectively taking the path of least resistance by going after unprotected accounts.
The Need for Identity Security
An identity security platform, which unifies proactive identity attack surface mapping and posture management with continuous identity threat detection and response, must sit as a layer on top of your IAM infrastructure.
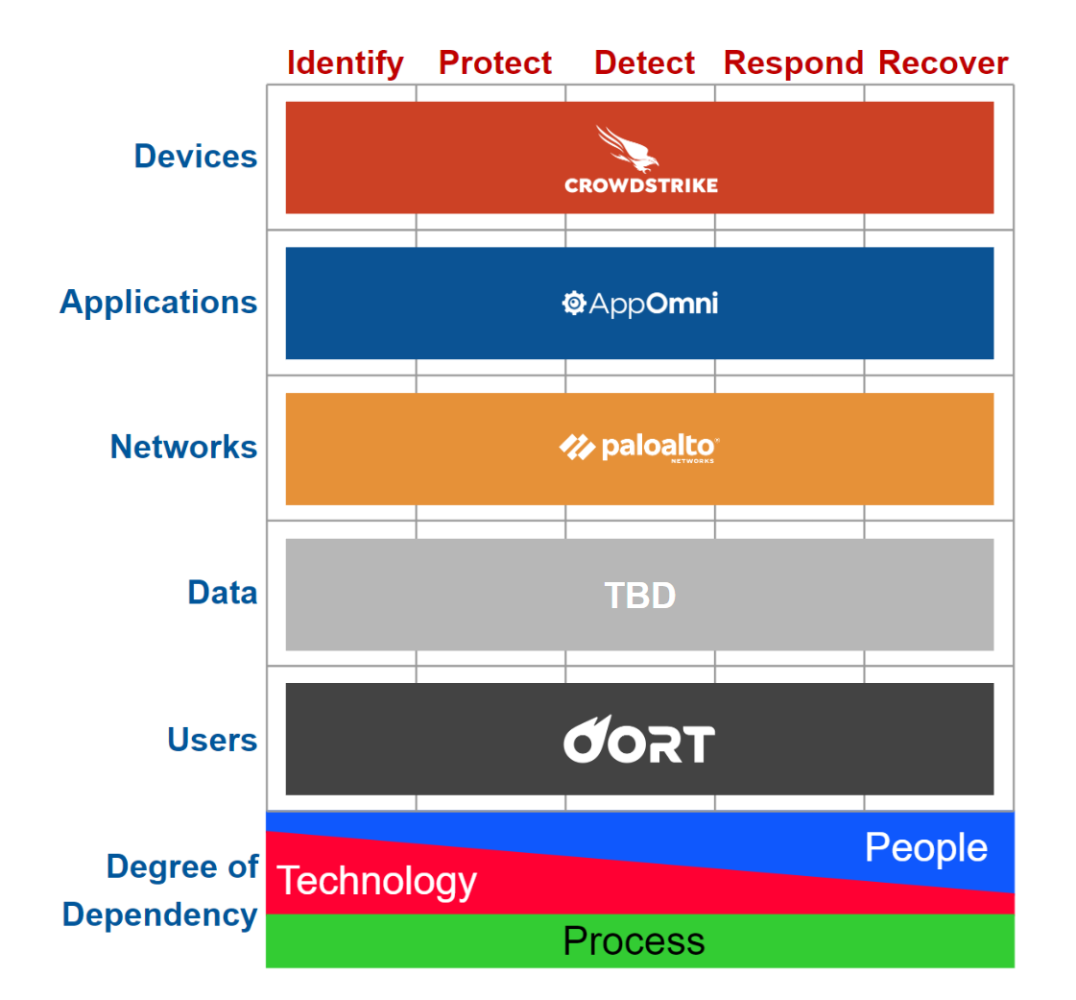
I’ve always loved the cyber defense matrix that Sounil Yu created as a mental model. For every cell of the matrix, you need coverage. The user / identity row is no different. Slotting in a few examples, application security (like AppOmni) has only recently reached a level of maturity that comes anywhere close to device security (like Crowdstrike) and network security (like Palo Alto Networks or Cisco or Zscaler). Identity security and data security are just getting started.
Oort’s Approach to Identity Security
Oort is that platform. A comprehensive solution for identity security that spans identity attack surface mapping, identity security posture management, and, of course, Identity Threat Detection and Response.
As we reflect back on the major breaches of 2022 and look toward the year ahead, the most mature security teams we encounter realize that comprehensive identity security is table stakes and a fundamental component of your modern security architecture.


